Huntress CTF 2025 - Tabby's Date
Recovered an unsaved Notepad note from Notepad TabState .bin backups by decoding UTF-16-LE and locating the Huntress CTF flag.
Huntress CTF: Tabby’s Date
Category: Forensics
Description: Ohhhh, Tab, Tab, Tab…. what has she done. My friend Tabby just got a new laptop and she’s been using it to take notes. She says she puts her whole life on there! She was so excited to finally have a date with a boy she liked, but she completely forgot the details of where and when. She told me she remembers writing it in a note… but she doesn’t think she saved it!! She shared with us an export of her laptop files.
Introduction
This write up covers the Tabby’s Date challenge from the 2025 Huntress CTF. Huntress CTF is a yearly CTF hosted by Huntress every October to celebrate cybersecurity awareness month, containing dozens of different challenges ranging from OSINT, to forensics, to full on web application penetration testing, and many more. To see my other write ups for this years CTF Click here.
Background
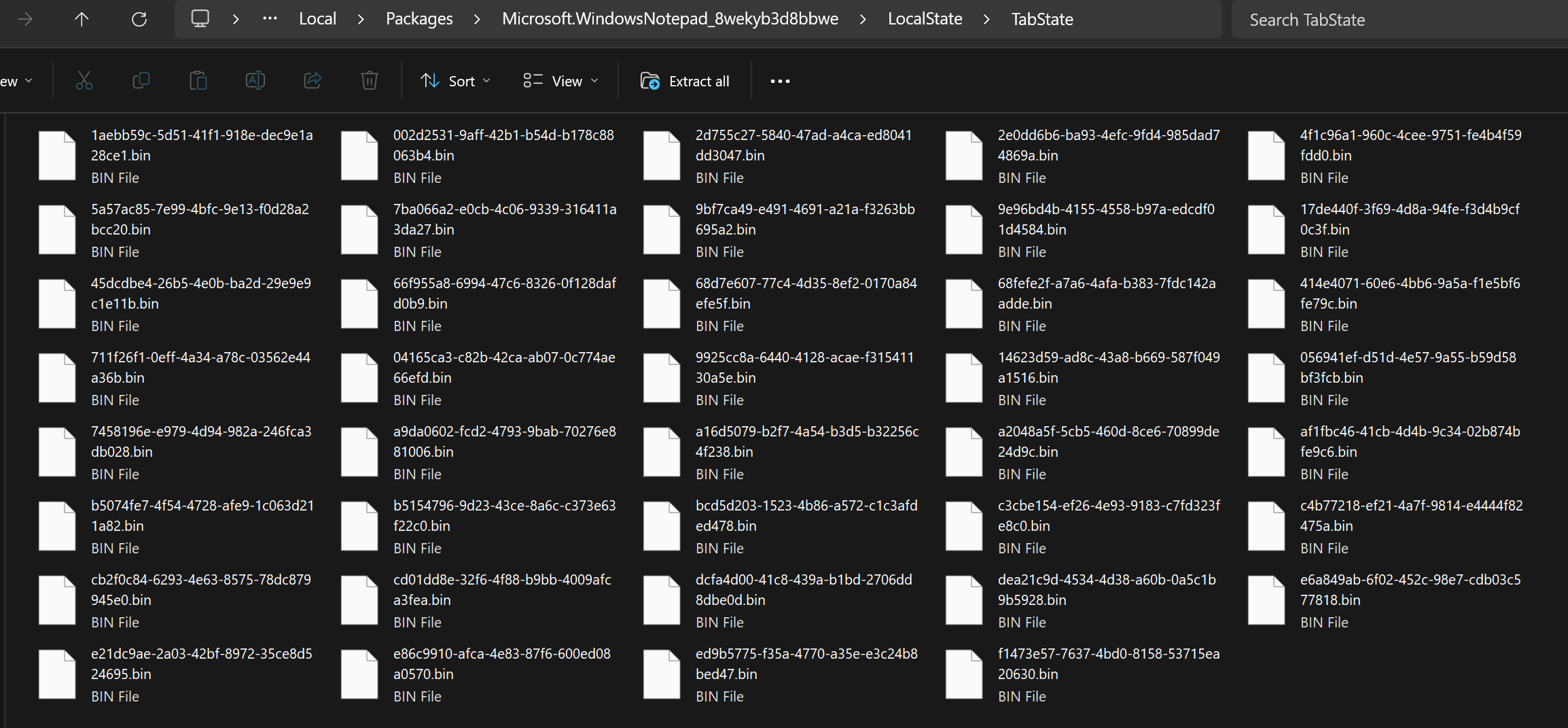
For this challenge we were told a user regularly uses her laptop for note taking and we needed to find information relating to date she has coming up. We were given a partial image of her Windows 11 system which was mostly empty and devoid of anything interesting. However, looking at the folder\C\Users\Tabby\AppData\Local\Packages\Microsoft.WindowsNotepad_8wekyb3d8bbwe\LocalState\TabState I found 39 .bin files which seemed interesting. This specific folder is the one Windows Notepad uses to store automatic tab state back ups of notes in case if the application closes without the user saving, meaning that even though they are .bin files they most likely contain readable ASCII text.
Finding the Flag
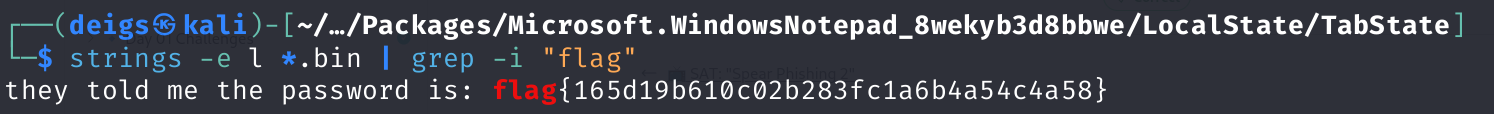
Copying the files over to my Linux machine I attempted to read one using the cat and strings commands, but it just returned gibberish, because Windows Notepad uses UTF-16 Little Endian encoding instead of the usual UTF-8. To overcome this I ran the strings command with the -e l flag for UTF-16 Little Endian, which allowed me to successfully read one of the notes. Figuring the flag would follow the usual Huntress CTF flag format of starting with the word “flag” I used this command to read through all the files and pipe the output into a grep search for the string “flag” strings -e l *.bin | grep -l "flag"